/ ¿Qué es la seguridad 5G?
¿Qué es la seguridad 5G?
La seguridad 5G es un área de seguridad de redes inalámbricas centrada en redes inalámbricas de quinta generación (5G). Las tecnologías de seguridad 5G ayudan a proteger la infraestructura 5G y los dispositivos habilitados para 5G contra la pérdida de datos, ataques cibernéticos, hackers, malware y otras amenazas. En comparación con las generaciones anteriores, 5G hace un mayor uso de la virtualización, la división de redes y las redes definidas por software (SDN), lo que la hace vulnerable a nuevos tipos de ataques.
¿Por qué es importante la seguridad 5G?
A medida que la tecnología 5G se implemente en daca vez más países, tendrá un impacto enorme en la infraestructura crítica y las industrias globales. Sin embargo, los avances tecnológicos de 5G también conllevan nuevos y mayores riesgos de ciberseguridad que los operadores de telecomunicaciones y sus clientes no pueden ignorar, entre ellos:
- Superficie de ataque ampliada: El aumento del número de dispositivos conectados y de infraestructuras que migran a la nube crea una gama más amplia de puntos de entrada que los ciberdelincuentes pueden explotar. Ya que la 5G permite interconectar millones de dispositivos por kilómetro cuadrado (frente a decenas de miles de dispositivos habilitados para 4G LTE y Wi-Fi), un dispositivo explotado podría generar vulnerabilidades en cascada que comprometan ecosistemas enteros.
- Vulnerabilidades de división de red: La infraestructura 5G permite la división de red, creando múltiples segmentos de red virtual uno al lado del otro en una red 5G, cada uno de los cuales responde a aplicaciones específicas, empresas o verticales de la industria. Esto es eficiente, pero abre la puerta a ataques dentro del segmento y otros riesgos nuevos. Los sectores deben aislarse y segmentarse de manera segura para evitar que los atacantes se muevan lateralmente.
- Riesgos de la cadena de suministro: La adopción de 5G depende de una cadena de suministro global de hardware, software y servicios. Garantizar la seguridad de todos los componentes es un desafío, ya que los malintencionados pueden intentar comprometer uno o más puntos de la cadena de suministro de hardware/software para infiltrarse en las redes y dispositivos 5G.
- Preocupaciones por la privacidad de los datos: Las redes 5G permiten el intercambio y el procesamiento masivo de datos, lo que crea problemas de privacidad en torno a las crecientes cantidades de datos personales/confidenciales implicados. El acceso no autorizado a los datos suele dar lugar a robos de identidad, fraudes y otros usos indebidos.
- Amenazas a la infraestructura crítica: A medida que la tecnología 5G se integra con la infraestructura crítica nacional, como redes eléctricas, sistemas de transporte e instalaciones de atención médica, una violación podría tener graves implicaciones para la seguridad pública, la salud de los pacientes, las operaciones industriales, la seguridad nacional o incluso la estabilidad económica.
Si bien la 5G está preparada para impulsar la próxima generación de transformación tecnológica en industrias, gobiernos y más, también conlleva riesgos de seguridad mayores (y en algunos casos, no cuantificados).
Beneficios de la seguridad 5G
Los proveedores de servicios y los operadores de redes móviles tienen la responsabilidad de garantizar la privacidad, seguridad e integridad de los datos y operaciones de los clientes en sus redes 5G. Al implementar las medidas de seguridad, los proveedores y operadores pueden:
- Aprovechar la supervisión y el análisis de seguridad en tiempo real para detectar y responder más rápidamente a posibles amenazas a la seguridad
- Minimizar el impacto de los ciberataques y reducir los costos asociados y el daño a la reputación
- Demostrar un compromiso con la integridad de datos y operaciones de los clientes, fortaleciendo su lealtad y confianza
Con la fabricación inteligente (Industria 4.0) en pleno apogeo, las empresas que utilizan dispositivos de Internet de las cosas (IoT) están muy interesadas en utilizar redes 5G para mantener sus dispositivos IoT conectados y funcionando.
¿Cómo funciona el 5G?
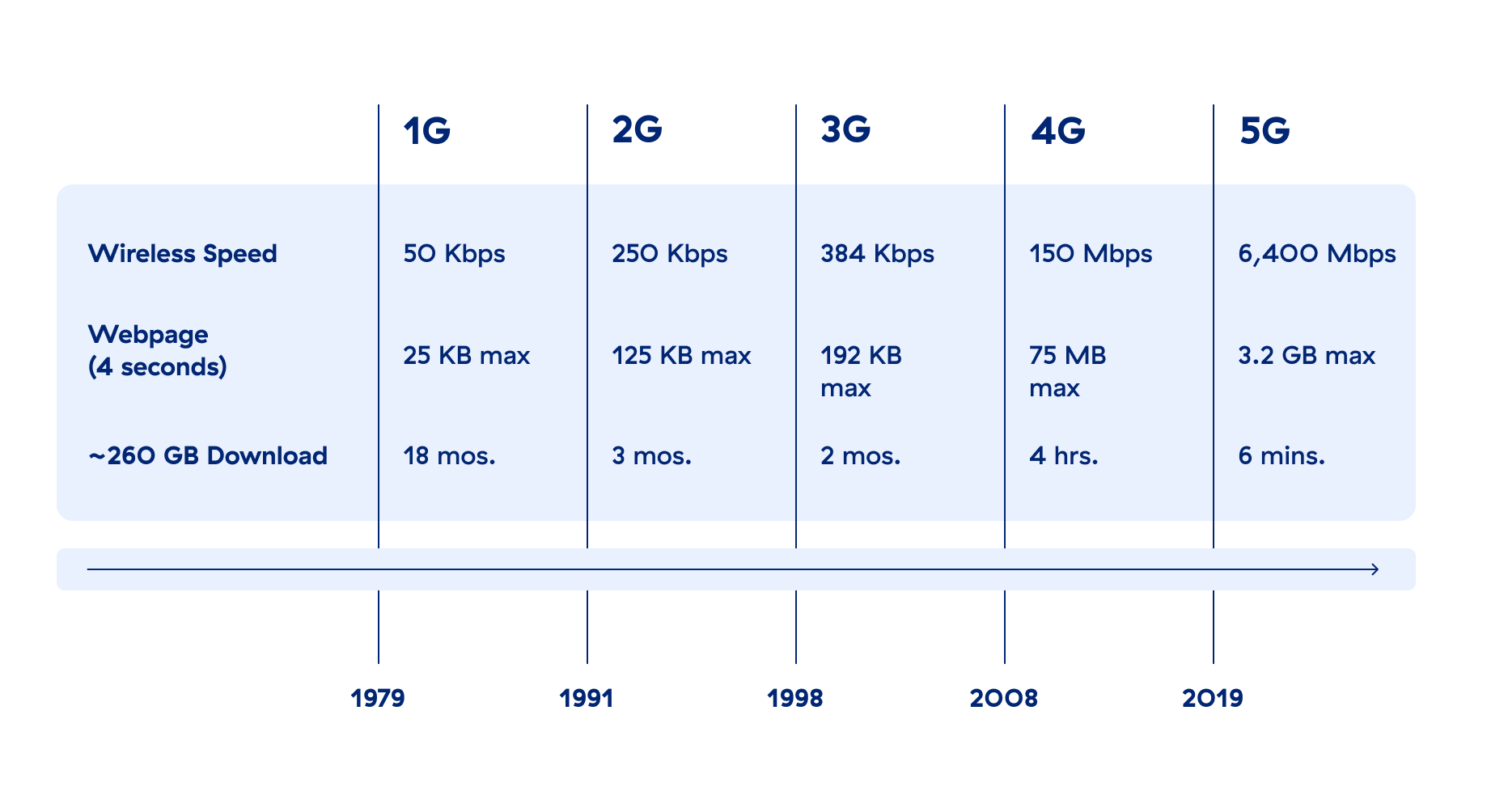
5G utiliza una amplia combinación de bandas de radio que impulsan velocidades de hasta 10 Gbps (de 10 a 100 veces más rápidas que 4G-LTE), lo que pronto hará que las experiencias web que hoy parecen suficientemente rápidas parezcan anticuadas. La 5G ofrece una latencia ultrabaja, lo que se traduce en un rendimiento de la red casi en tiempo real. Si bien, antes un paquete de datos podía tardar entre 20 y 1000 milisegundos (ms) en llegar desde su laptop o teléfono inteligente a una carga de trabajo, la 5G puede reducir ese tiempo a unos pocos milisegundos cuando el caso de uso lo exige.
Pero, eso no es todo: La velocidad física por sí sola no reduce la latencia. Varios factores, como la distancia, la congestión del ancho de banda, las deficiencias de software y procesamiento, e incluso los obstáculos físicos, pueden contribuir a una alta latencia.
Para lograr una latencia ultrabaja, lo que más necesitan los recursos informáticos es estar más cerca de los dispositivos del usuario final. Tener servidores ubicados físicamente cerca de los dispositivos del usuario final se denomina "Edge compute" (computación periférica). El tipo de cálculo de Edge varía según el rango de latencia:
- Far Edge: Latencia entre 5 y 20 ms; más alejado de la nube y más cercano a los dispositivos
- Near Edge: Latencia de más de 20 ms; más cerca de la nube que de los dispositivos
- Deep Edge: A menos de 5 ms de los dispositivos
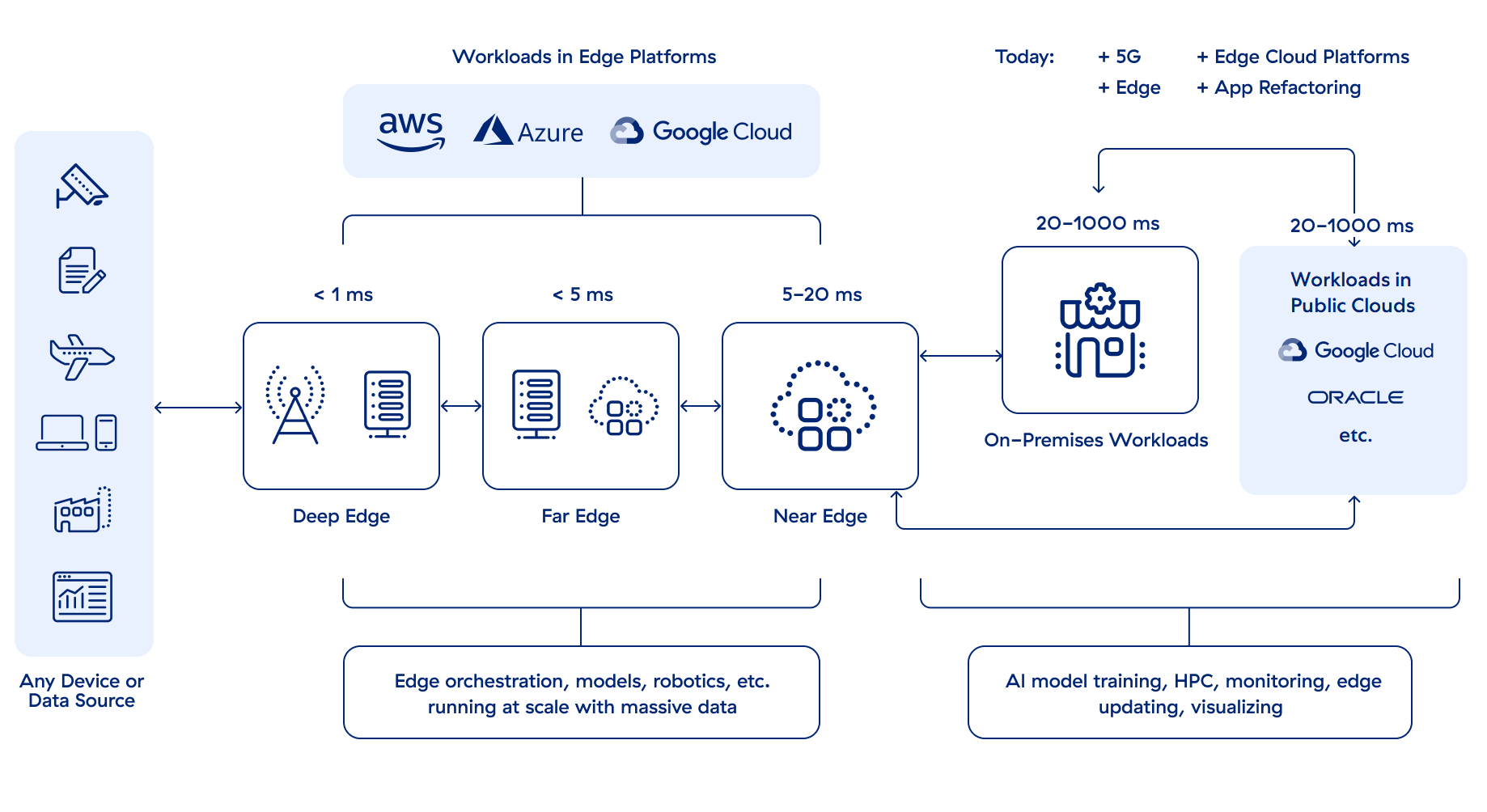
Un esquema de red 5G básico: ¿Dónde comienza (o termina) su red?
El caso de uso, los requisitos de latencia y el presupuesto influyen en el nivel de Edge compute que se necesita. No todo requiere un rendimiento casi en tiempo real, pero muchas cosas necesitan un "tiempo real suficientemente bueno", para lo cual unos 20 ms bastarían.
La 5G también está diseñada para ser ampliamente escalable para dispositivos conectados. Las redes de acceso de radio mejoradas pueden admitir 1000 veces más ancho de banda por unidad de área y 100 veces más dispositivos conectados que la 4G LTE. Los dispositivos móviles de consumo, los dispositivos empresariales, los sensores inteligentes, los vehículos autónomos, los drones y más pueden compartir la misma red 5G sin degradación del servicio.
Comparación entre 5G y 4G
Tanto la 4G como la 5G son tecnologías de telecomunicaciones inalámbricas de alta velocidad para dispositivos móviles.
En términos de capacidades técnicas, la 4G ofrece velocidades de transmisión de datos de hasta unos 100 Mbps, mientras que la 5G puede ofrecer hasta 20 Gbps. Para las comunicaciones entre dispositivos, la latencia de 4G oscila entre unos 60-100 milisegundos, mientras que 5G puede ofrecer una latencia mucho menor, potencialmente inferior a 5 milisegundos. Y en lo que respecta al ancho de banda y al volumen de conexiones, una red 4G puede admitir varios miles de dispositivos en un kilómetro cuadrado, mientras que una red 5G puede admitir un millón.
La infraestructura más compleja de la 5G también amplía su superficie de ataque, sin embargo, (y con muchos más dispositivos conectados y velocidades de transferencia de datos mucho más rápidas que la 4G) la 5G es significativamente más vulnerable a los ciberataques. Además, el uso de nuevas tecnologías como la virtualización y las redes definidas por software en las redes 5G puede dar lugar a nuevas vulnerabilidades que los malintencionados podrían explotar.
Por último, estas son las diferencias más críticas entre generaciones: La 5G funciona en el perímetro de la red, no dentro de la infraestructura tradicional en la que se basa la 4G. Por extensión, la seguridad no puede ser aplicada eficazmente por la infraestructura de red tradicional y, en su lugar, debe aplicarse también en el perímetro de la red.
Analicemos a continuación la 5G con respecto a Edge computing y el perímetro.
¿Cómo funciona 5G con Edge Computing?
La tecnología 5G y el edge computing (computación distribuida que permite el procesamiento y almacenamiento de datos en el perímetro de la red) están transformando la manera en que nos comunicamos y hacemos negocios. Las mejoras en la velocidad, la transmisión de datos en tiempo real y la densidad de la red móvil son las piedras angulares de la conectividad moderna, ya que proporcionan la capacidad esencial para los dispositivos conectados al IoT, la automatización, las interfaces de realidad virtual y aumentada, las ciudades inteligentes y mucho más.
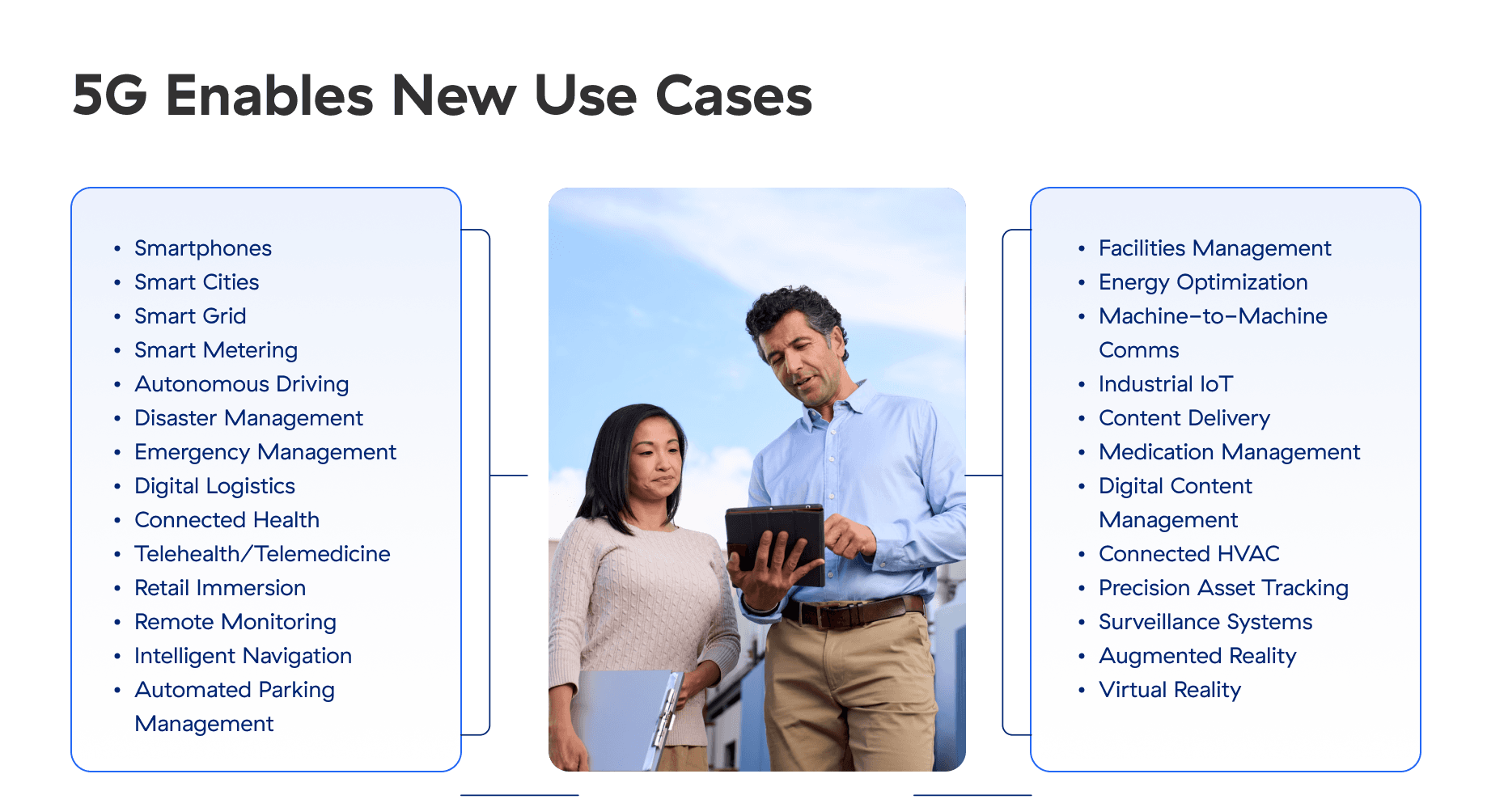
En efecto, la 5G proporciona la conectividad de alta velocidad y la baja latencia necesarias para que el edge computing funcione con eficacia. Los datos pueden transmitirse y recibirse casi al instante, lo que permite la comunicación y el análisis en tiempo real para dar soporte a servicios en los que el tiempo es un factor crítico y a otras aplicaciones que requieren una respuesta inmediata, como algunas funciones de la Industria 4.0.
Entre otros muchos factores del diseño de la red 5G, la proximidad física al dispositivo es clave para lograr una baja latencia. Esto significa que la infraestructura de la red central, el servidor de aplicaciones y, sobre todo, la infraestructura de seguridad deben trasladarse de los centros de datos centralizados al perímetro de la red, más cerca de los usuarios. Para ello, las organizaciones deben recurrir a Zero Trust.
Problemas de seguridad del 5G
El estándar 5G señala explícitamente que la seguridad es un principio de diseño clave. Esto normalmente significa que leerá que "5G es seguro por diseño". En otras palabras, la 5G se diseñó para ser segura.
La realidad es que la seguridad de la 5G se limita a la propia red. No se extiende a los dispositivos y cargas de trabajo que los clientes utilizarán para comunicarse a través de una red 5G.
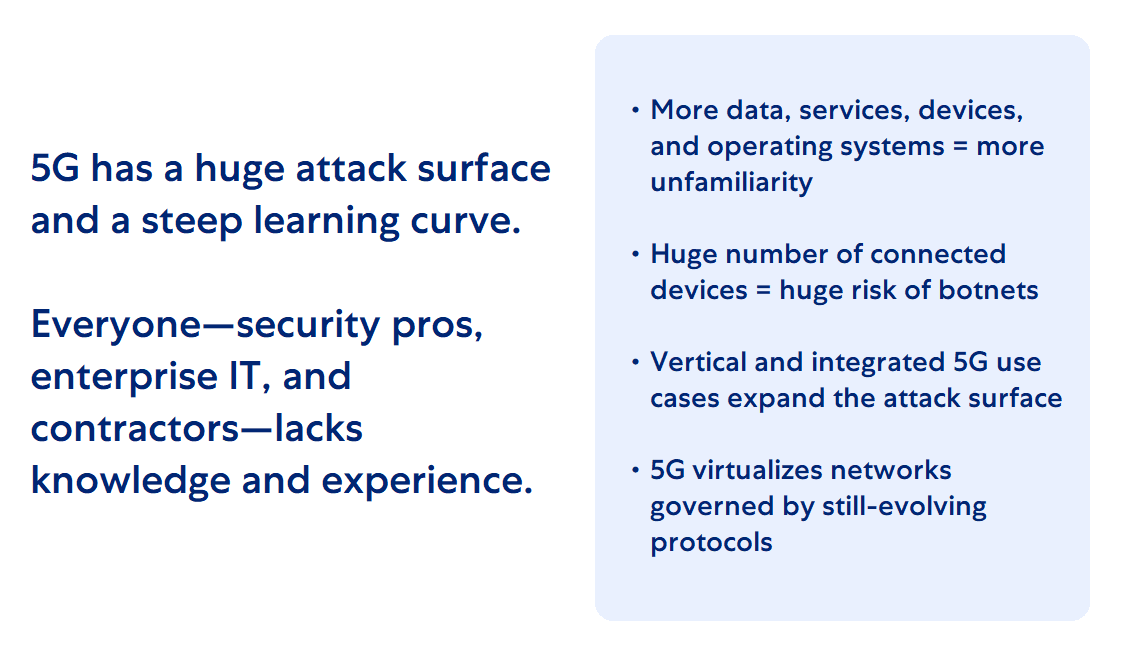
Así, mientras que 5G significa más datos, servicios, dispositivos, sistemas operativos, virtualización y uso de la nube, también significa que la superficie de ataque 5G es enorme, y las cargas de trabajo Edge son los nuevos objetivos preferidos de muchos atacantes.
La seguridad 5G plantea una pronunciada curva de aprendizaje, y muchos profesionales de la seguridad, TI empresarial y subcontratistas carecen de los conocimientos y la experiencia necesarios para proteger las aplicaciones que se ejecutan en redes 5G. Al ser la unión de sistemas informáticos de gran escala con redes de telecomunicaciones inalámbricas, la 5G necesita especialistas en ciberseguridad expertos en ambos mundos.
5G y confianza cero para máxima seguridad
Zero Trust simplifica la protección de las cargas de trabajo y los dispositivos 5G/edge, por lo que las organizaciones que la adopten se darán cuenta de que incorporar la 5G, aún con los desafíos de seguridad que conlleva, es más fácil, rápido y seguro.
Zero Trust es la arquitectura para una supervisión exhaustiva de la seguridad, controles de acceso granulares basados en el riesgo, automatización de la seguridad del sistema coordinada en toda la infraestructura y protección en tiempo real de los activos de datos críticos en un entorno dinámico de amenazas.
Cómo puede ayudar Zscaler: Adopte el modelo de seguridad de cofianza cero
La arquitectura Zscaler Zero Trust para 5G privada protege y simplifica las implementaciones privadas de 5G para el núcleo centralizado de 5G, lo que ayuda a los proveedores a:
- Permitir la conectividad de Zero Trust: Asegure la conectividad de sitio a sitio a través de Internet sin una red enrutable (5G UPF a Core), y garantice que los usuarios y dispositivos (UE) no estén en la misma red enrutable que las aplicaciones en el MEC, DC y la nube.
- Asegurar aplicaciones y datos: Minimice la superficie de ataque de entrada y salida e identifique vulnerabilidades de cargas de trabajo, configuraciones erróneas y permisos excesivos.
- Asegurar las comunicaciones: Evite el compromiso y la pérdida de datos con la inspección de contenido en línea.
- Gestionar la experiencia digital: Resuelva rápidamente problemas de rendimiento con visibilidad del rendimiento del dispositivo, la red y las aplicaciones.
Los conectores de aplicaciones, los conectores de sucursales y los conectores de nube de Zscaler Private Access, junto con Zscaler Client Connector, pueden proteger los dispositivos y las cargas de trabajo de los clientes en las redes 5G actuales. A mediados de 2023 se lanzó una versión de Branch Connector diseñada para proteger las tecnologías centrales 5G de violaciones, y en 2024 se implementarán más mejoras.





