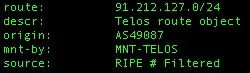
 A detailed analysis was provided, here, on the new version of the Storm Worm making it's rounds this week. I went looking in our logs for HTTP POSTs to three and four character GIF and JPG files with relatively small request and response sizes (<1000 bytes). What I found was a number of transactions to 91.212.127.114 (on Telos, no PTR record).
A detailed analysis was provided, here, on the new version of the Storm Worm making it's rounds this week. I went looking in our logs for HTTP POSTs to three and four character GIF and JPG files with relatively small request and response sizes (<1000 bytes). What I found was a number of transactions to 91.212.127.114 (on Telos, no PTR record).
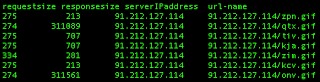
A small snippet of transactions:
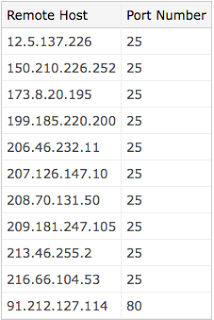
There is a ThreatExpert report on the related server / malware, which is identified as Email-Worm.Zhelatin (name used by Kaspersky and F-Secure for the Storm Worm). The infected hosts connect out to mail servers in attempts to mass-mail and infect others. Here is a list of some of the email servers that it connects to:
Keep an eye out for these types of transactions within your networks.
Blog de Zscaler
Reciba las últimas actualizaciones del blog de Zscaler en su bandeja de entrada
SuscribirseStorm Worm 2.0
Gracias por leer
¿Este post ha sido útil?

Reciba las últimas actualizaciones del blog de Zscaler en su bandeja de entrada
Al enviar el formulario, acepta nuestra política de privacidad.




